Secure JTAG
Most embedded devices provide a JTAG interface for debugging purposes. However, if left unprotected, this interface can become an important attack vector on the system. The i.MX6 series System JTAG Controller (SJC) allows you to regulate JTAG access with three security modes using OTP (One Time Programmable) eFuses:
- Disable:
- Disabled JTAG: This mode provides maximum security. All security-sensitive JTAG features are permanently blocked, preventing any debug. This mode is not recommended as boundary scan is currently used by Digi on its manufacturing process and could affect the RMA procedure.
- Disabled debugging: This mode disables debugging but leaves the boundary scan functionality enabled. This is the recommended mode for maximum security.
- Enabled: This mode provides low security. This is the default mode of operation.
- Secure: This mode provides high security. JTAG use is regulated by a 56-bit secret key-based challenge/response authentication mechanism.
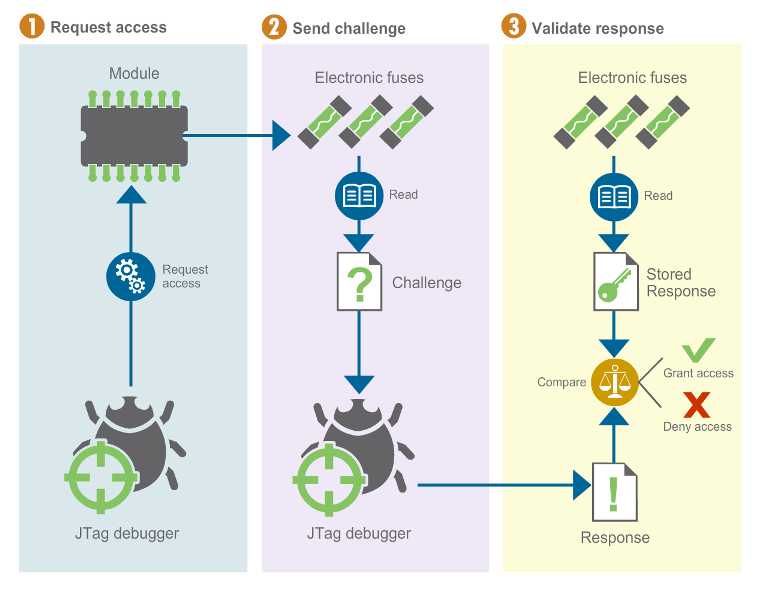
The response key must be programmed in the target and configured in the debug tool.



