Cybersecurity expectations for connected healthcare products have changed. A
medical device software bill of material (SBOM) is no longer a document created for regulatory review and then forgotten. It has become a practical, day-to-day tool that helps manufacturers manage risk, protect patients and maintain compliance over a product’s entire lifecycle.
As discussed in a recent webinar hosted by the IoT M2M Council and sponsored by Digi, regulators now expect medical device manufacturers to demonstrate ongoing cybersecurity maturity. In the U.S., FDA requirements written into law require proof of post-market monitoring, vulnerability disclosure and the ability to update devices already deployed in the field. Europe is following a similar path with MDR and NIST 2.0 obligations. In this environment, a static SBOM does not go far enough.
Here’s a **Google featured snippet–optimized AI Overview** (tight, definitional, and skimmable), followed by **copy-paste HTML** you can drop into the blog post (as a reusable “AI Overview” module). I’m writing this to be useful for both classic featured snippets and AI Overviews: short lead answer, clear headings, bullets, and direct phrasing.
AI Overview: Medical Device SBOM
A medical device Software Bill of Materials (SBOM) is a structured inventory of all software components in a connected healthcare product—open source, third-party and proprietary code—plus versions and licenses. Used as a living artifact, an SBOM helps medical OEMs quickly determine whether newly disclosed vulnerabilities (CVEs) affect specific device builds and deployed systems, supporting ongoing cybersecurity and compliance across the product lifecycle.
Why a medical device SBOM matters
- Faster vulnerability impact analysis: Map SBOM components to CVEs to see what actually applies to your device configuration.
- Better remediation prioritization: Reduce alert noise by focusing on exploitable, relevant issues rather than every theoretical match.
- Lifecycle cybersecurity readiness: Maintain traceability and evidence of monitoring, assessment and mitigation over time.
- Regulatory alignment: Supports expectations for ongoing post-market cybersecurity maturity and transparency.
Static vs. living SBOM
A static SBOM is generated once and quickly becomes outdated. A living SBOM is automatically regenerated during the build/release process and continuously monitored against new CVEs—critical for long-lived, field-deployed medical devices.
How to operationalize SBOMs in connected systems
- Automate SBOM generation in CI/CD for every release.
- Link SBOM data to vulnerability intelligence (CVE identifiers, severity, and exploit context).
- Filter by real device context (configuration, enabled features, deployed versions) to reduce false positives.
- Enable secure remote updates so patches can be delivered to devices already in the field.
Key takeaway
An SBOM is no longer just a compliance document. For medical OEMs building connected healthcare products, treating the SBOM as an operational security tool enables faster response to vulnerabilities, safer patching and sustained trust over the device’s full lifecycle.
Jump to:

A medical device SBOM starts as an inventory of software components, including open source packages, third-party software and internally developed code. Version data and licensing details are also required. This information forms the baseline needed to understand whether a newly disclosed vulnerability applies to a specific product.
However, inventory alone does not address real-world risk. To be useful, a medical device SBOM must connect directly to vulnerability intelligence. That means linking SBOM data to CVE identifiers and severity scores, then filtering out issues that do not apply to the device’s configuration. Without this context, teams often face hundreds or thousands of alerts with little guidance on what actually requires action.
One of the key themes from the webinar was that an SBOM must be treated as a living artifact. Instead of generating it once at product launch, manufacturers should integrate SBOM creation into the build process and update it automatically with every software release.
This approach supports continuous vulnerability monitoring throughout the product life cycle. As new CVEs emerge, teams can quickly determine whether deployed devices are affected and prioritize remediation based on risk. For long-lived medical devices, this ongoing visibility is essential.
A mature medical device SBOM process also supports regulatory expectations for traceability and transparency. Manufacturers can show how risks were identified, assessed, mitigated and monitored over time rather than reacting only when an issue becomes public.
Effective SBOM use requires more than tooling. It depends on embedding security practices directly into the software development life cycle. This includes automated scanning, curated vulnerability reporting and clear guidance on remediation steps.
Recorded webinar: IoT Security is a Journey, NOT a Destination
During the webinar, Digi in collaboration with ByteSnap shared a practical example of how OEMs can manage this process at scale. By combining automated SBOM generation, ongoing CVE analysis and tested security updates, teams reduce the effort required to stay compliant while lowering the risk of introducing new issues during patching.
Ultimately, a medical device SBOM supports more than compliance. It helps manufacturers protect patient safety, safeguard sensitive data and preserve trust in connected healthcare technologies. As cybersecurity requirements continue to evolve, treating the SBOM as an operational security tool rather than a checkbox will be critical to long-term success.
Equally important, an SBOM strengthens transparency across the medical device software supply chain. By maintaining clear visibility into the components and dependencies within a device, manufacturers can more confidently assess risk, respond to emerging threats and communicate with regulators, healthcare providers and partners. This transparency enables faster incident response, more informed security decisions and better collaboration across the ecosystem. Over time, these capabilities help medical OEMs demonstrate a proactive commitment to cybersecurity, reinforcing confidence in the reliability and safety of their connected products.
Discover How Digi ConnectCore Solutions Can Help
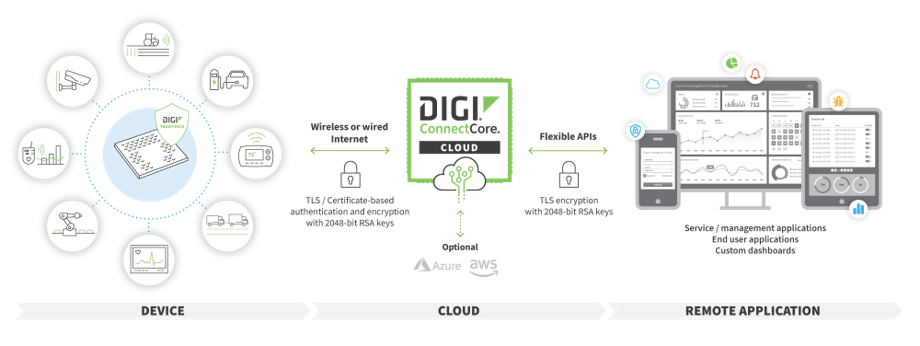
Medical OEMs building connected systems for the healthcare vertical — as well as other developers — must increasingly meet the requirements of regulations like the EU Cyber Resilience Act. These emerging regulations require OEMs to integrate ongoing remote management abilities into their embedded devices to support remote firmware updates and ongoing security management.
The Digi ConnectCore ecosystem is designed to support these requirements, ensuring OEMs, and/or their end customers, can maintain their devices after deployment and over their entire lifecycle. Learn more by visiting our Digi ConnectCore Security Services page.
Frequently Asked Questions: Medical Device SBOMs
What is a software bill of materials (SBOM) in a medical device?
A software bill of materials (SBOM) is a structured inventory of all software components used within a medical device. This includes open source libraries, third-party software, operating system components and internally developed code. An SBOM typically records component names, versions, dependencies and licensing information.
For medical OEMs developing connected systems, the SBOM provides visibility into the software supply chain so teams can quickly determine whether newly discovered vulnerabilities affect a deployed product.
Why are SBOMs becoming mandatory for medical device manufacturers?
Cybersecurity requirements for medical devices have expanded significantly. Regulators increasingly expect manufacturers to demonstrate ongoing risk management throughout a product’s lifecycle.
In the United States, the FDA now requires manufacturers of connected medical devices to show evidence of:
- Continuous cybersecurity monitoring
- Vulnerability management processes
- Coordinated vulnerability disclosure
- The ability to update devices already deployed in the field
Similar expectations are emerging in Europe through frameworks such as the Medical Device Regulation (MDR) and broader cybersecurity initiatives. SBOMs help manufacturers demonstrate the transparency and traceability regulators expect.
How does an SBOM improve medical device security?
An SBOM improves security by giving manufacturers a clear view of every software component in their device. When a vulnerability is publicly disclosed, teams can quickly determine whether the affected component exists in their product and whether remediation is required.
Without an SBOM, this process can take days or weeks of manual investigation. With a well-maintained SBOM connected to vulnerability intelligence feeds, the analysis can happen in minutes.
This faster response helps reduce risk to patients, healthcare providers and hospital networks.
What makes a medical device SBOM “living” rather than static?
A static SBOM is generated once — typically during product launch — and rarely updated afterward.
A living SBOM is integrated directly into the software development pipeline and automatically updated with every build or release. This approach allows manufacturers to continuously monitor vulnerabilities, track component changes and maintain an accurate record of the software environment throughout the product lifecycle.
For long-lived medical devices that may remain deployed for 10 years or more, this continuous visibility is essential.
How are SBOMs connected to vulnerability databases like CVE?
To become actionable, SBOM data must be correlated with vulnerability intelligence sources such as the Common Vulnerabilities and Exposures (CVE) database.
Security tools compare the component versions listed in the SBOM with known vulnerabilities. They then determine:
- Whether the vulnerability applies to the specific component version
- Whether the vulnerable code path is actually used
- The severity and exploitability of the issue
This contextual analysis helps security teams prioritize the issues that truly affect the device instead of responding to every alert.
When should SBOM generation occur during development?
Best practice is to generate SBOMs automatically during the build process as part of the software development lifecycle.
This ensures that:
- Every release includes an up-to-date SBOM
- Component changes are tracked over time
- Security and compliance teams have immediate visibility into new dependencies
Automated SBOM generation also reduces manual effort and improves consistency across development teams.
What challenges do OEMs face when implementing SBOM processes?
Many medical OEMs encounter several practical challenges when operationalizing SBOMs:
- Managing large volumes of vulnerability alerts
- Distinguishing relevant vulnerabilities from false positives
- Maintaining SBOM accuracy across multiple product versions
- Coordinating remediation across development and security teams
Automation and integrated security workflows can significantly reduce these burdens.
How do SBOMs support long-term device lifecycle management?
Medical devices often remain in service for many years after deployment. During that time, new vulnerabilities will inevitably emerge in underlying software components.
A well-maintained SBOM enables manufacturers to:
- Identify affected devices quickly
- Prioritize remediation based on risk
- Deliver targeted security updates
- Document cybersecurity management for regulators
This ongoing visibility helps manufacturers maintain both compliance and patient safety over the entire lifecycle of the device.
How do remote device management capabilities relate to SBOMs?
An SBOM helps manufacturers identify vulnerabilities, but remediation often requires updating devices in the field. For connected medical systems, this typically means secure remote firmware updates.
Platforms that support device monitoring, secure update delivery and lifecycle management allow manufacturers to respond quickly when vulnerabilities are discovered in SBOM components.
How can Digi help medical OEMs address SBOM and cybersecurity requirements?
Digi’s embedded and IoT platforms are designed to support secure device lifecycle management. Solutions such as the Digi ConnectCore ecosystem provide capabilities that help OEMs:
- Maintain visibility into deployed devices
- Deliver secure remote firmware updates
- Manage device security throughout the lifecycle
- Support compliance with emerging regulations such as the EU Cyber Resilience Act
These capabilities help medical device manufacturers translate SBOM insights into practical security operations.
Next Steps