Welcome to our series on IoT device management. As the Internet of Things grows, and device networks and edge computing architectures become more complex, it is important to be able to manage all those devices across the network. You need network monitoring tools that automatically thwart vulnerabilities and give you control of your entire deployment, no matter how vast or geographically distributed.
Digi Remote Manager® (DRM) is a secure platform for monitoring and controlling distributed IoT devices. Once you have more than a few devices in your Internet of Things deployment, the challenge of configuring and managing those devices grows. You may be asking these questions:
- How do I update firmware across my entire device network?
- How do I roll out security patches?
- If one or more devices are subject to malicious tampering, how will I know? And is there an automated way to fix it?
- What if I want to roll out some new functionality to my devices?
- Is there a way to get a view into the status of all of my devices, and what is the best way to do network performance monitoring?
DRM is designed to solve these issues, give you visibility into your your entire device network, provide alerts for proactive management of network connectivity and performance problems, improve your networks security, and put you in control of your devices and edge compute application logic.
Our VP of Product, Scott Nelson, came up with the analogy recently that DRM is the "Quarterback of the Stack." By this he means DRM is like the most important player on the field, driving and coordinating all of the other players in the stack to create a cohesive performance of all players. Without DRM playing this vital function in the IoT stack, the various components and ecosystem partners of the stack dont get the data or instruction they need to know which actions to take.
Lets explore what we mean by the "IoT stack" and some of the core functionality of DRM.
A Visual Representation of the IoT Stack
For discussion purposes, lets look at the collection of applications, services, tools and hardware that make up the IoT stack.
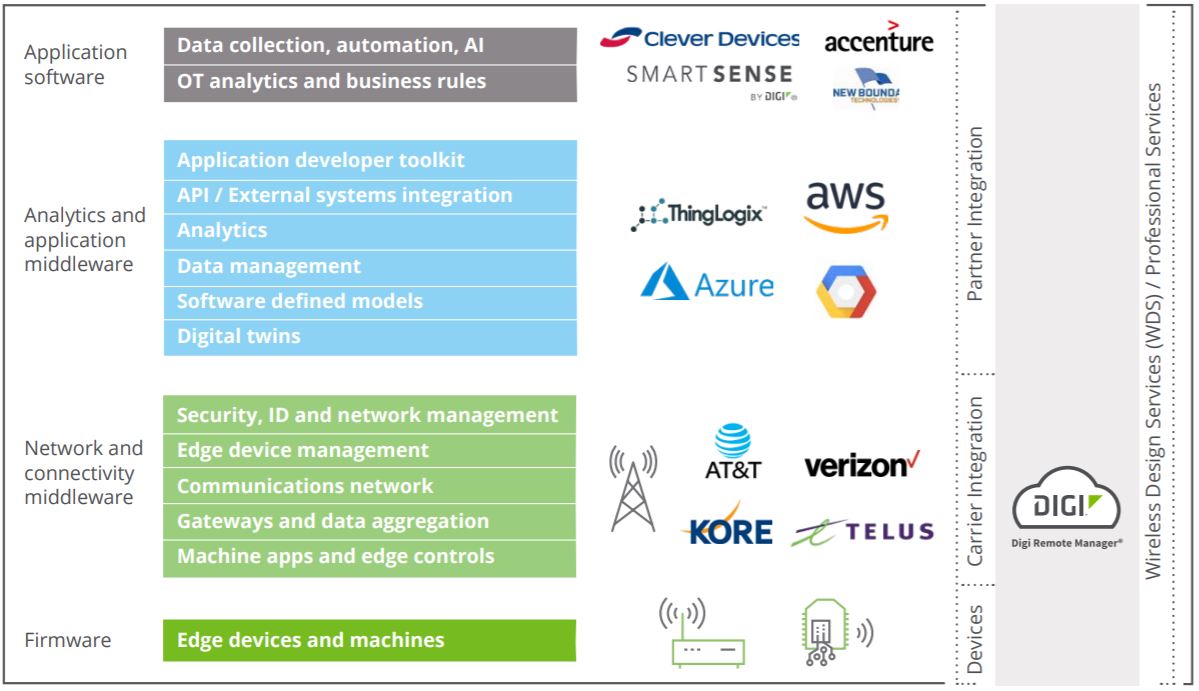
We will be talking about the IoT stack in this and future posts, and it helps to see all the different pieces involved. Digi Remote Manager touches or coordinates nearly all of these layers.
Managing the Security of Your Device Network
IoT security is a complex undertaking, but Digi Remote Manager offers some critical functionality that provides visibility into your network and simplifies management of your network security.
Here are some highlights:
- An administrator first establishes profiles for the devices on your network. For example, they can specify an approved configuration including device settings, firmware version and edge logic programs.
- DRM automatically checks to ensure those device configurations remain as established in the device profile. It will alert you if there has been a change, and if you choose, set it back to the authorized configuration.
- DRM verifies that any edge software you have deployed is the version you intended, ensuring that it has not been tampered with.
- Additionally, an administrator can restrict or quarantine devices that are suspect for further analysis. Once restricted, the device has limited functionality, to prevent a security breach
Managing Edge Program Logic
You can enhance the functionality of your devices using files that you distribute to them using Digi Remote Manager. For example, if you want to update program logic, you can use DRM to automate that process.
The method is similar to the process described earlier for managing your IoT device security. First, you create a profile containing the application logic you want to distribute. DRM will detect that the deployed version is outdated and will update your devices to run the new version that you specified.
Integrating with Third-Party IoT Cloud Platforms
Digi Remote Manager facilitates integration with a range of third-party platforms that you may connect with for additional functionality such as analytics, data visualization, and other business application integration. This feature of DRM allows you to connect to the cloud provider of your choice. DRM is cloud agnostic, so it is not tied to any particular provider.
For example, you can integrate with third party applications by configuring DRM to forward data to one of those applications using the push monitor feature.
Alternatively, you can use DRM to load application logic, combined with provided libraries, to connect devices directly to third-party IoT platforms.
Performing Mass Firmware Updates
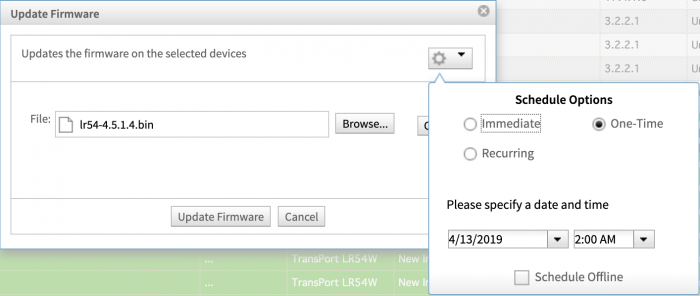 A key feature of Digi Remote Manager is the ability to update firmware on a mass scale. Once you tell DRM what you want it to do, it automates the updates to all specified devices or device groups.
A key feature of Digi Remote Manager is the ability to update firmware on a mass scale. Once you tell DRM what you want it to do, it automates the updates to all specified devices or device groups.
You have several choices for how to roll out a firmware update. Here are a few examples:
- Manually select the devices you want to update and then select the firmware update action.
- Create a schedule that will perform the update at a specified time in the future.
- Create a profile that will manage the firmware update by ensuring that any device that is in scope of the profile is updated.
DRM offers the flexibility to set up firmware updates however it suits your short-term and long-term needs. For example, you might want to deploy updates to a test group prior to mass deployment. Or you may want to update firmware on all devices in a specified geographic region.
Gaining Visibility into Device Health and Performance
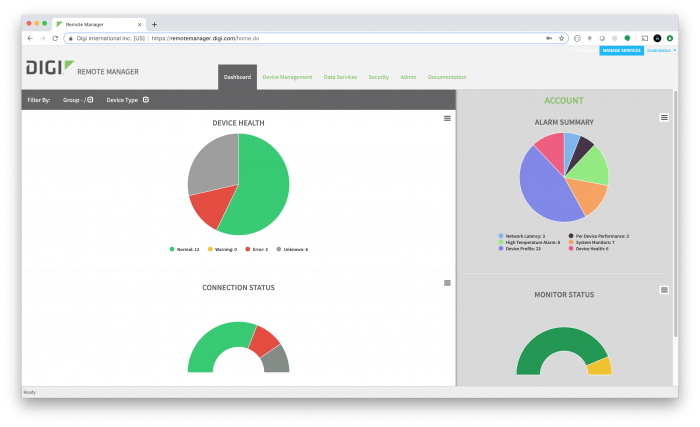
The DRM dashboard lets you see at a glance whether any of your devices are showing signs of connectivity or performance problems, to aid in troubleshooting.
You can also set up alerts for certain conditions, and then quickly drill down to troubleshoot the cause. Here are a few scenarios:
- One or more devices are suddenly disconnected. You may determine that they are all in the same area, and may therefore indicate a cellular outage.
- One or more devices stop working reliably or are connecting intermittently. You may see that the behavior has changed, but they are stationery (non-mobile) devices. You can then troubleshoot further:
- If you notice that the signal quality has deteriorated at a remote site, you can evaluate the historical readings to see whether the issue occurred on a certain date.
- At this point you might want to work with an on-site administrator and determine if something new was installed that is causing radio frequency noise. You may need to reconfigure the antennas at that site.
You can gain visibility into the status of your devices regardless of the number of devices in your network, or where they are installed.
Depending on your cellular carrier and your administrative policies, you may be able to perform out-of-band management of remote devices that are having trouble connecting. For example, DRM supports SMS access to devices, if supported by your carrier. This would allow you to send a message to a device to determine whether or not it is in a normal connected state.
Managing Cellular Carriers
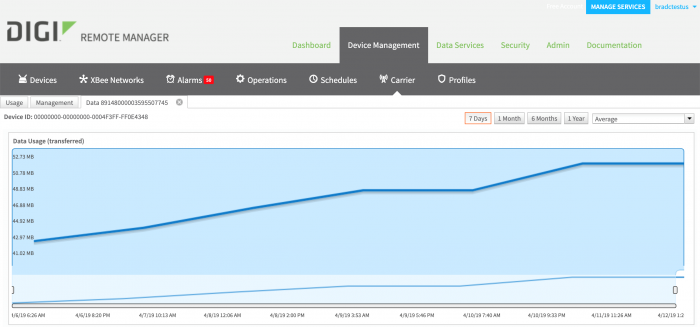
DRM has the ability to connect to many cellular carriers, including AT&T, Verizon and others through partnerships. Since data plans usually have a limit (for example, 10 MB month), it is important to manage your cellular data usage.
You can configure DRM to connect to your cellular carrier to monitor data usage on your devices. As each device is connected to DRM, the SIM ID is matched to the DRM device ID. This provides visibility and management of every device in your network, allowing you to determine your exact usage, by device. You can then set alerts based on actual data usage, according to the carrier.
Whats Next
Digi is continually enhancing the Digi Remote Manager dashboard, features and user experience to make it as easy as possible to perform these complex tasks across an IoT device deployment, regardless of its size or how geographically dispersed it may be. Contact Digi if you would like more information on how DRM can support your IoT device security and network management goals or to start a free trial.
In our next post in this series, we will be talking about the integration with third party IoT services in the analytics and application middleware layer of the IoT stack.